SIM swapping is a growing crime and it's easy to become a victim. How to stay safe

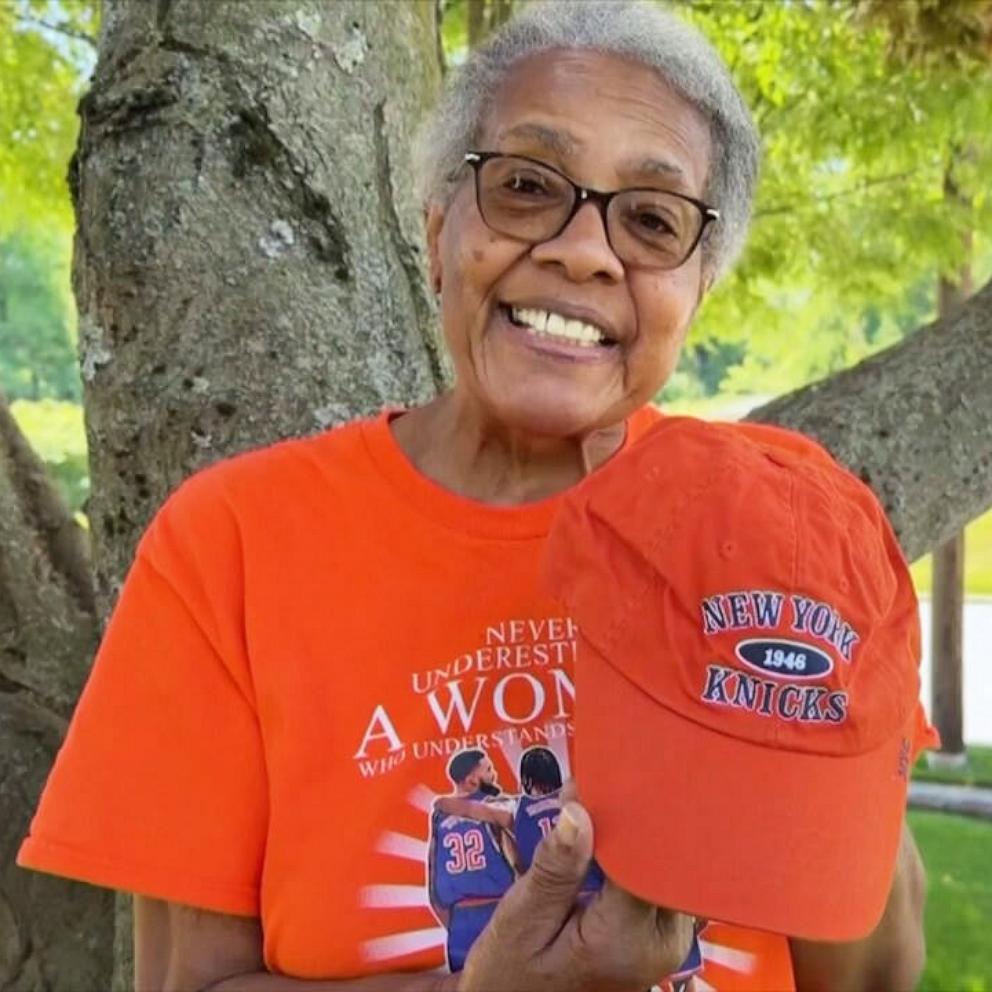
Robert Ross had never heard of the crime of “SIM swapping” until he became a victim.
“I saw a notification for a withdrawal request from one of my financial institutions,” the tech executive told ABC News. “And I thought, ‘That's weird. I didn't make a withdrawal request.’”
Within 20 minutes, years of savings -- nearly $1 million -- had been wiped out.

“And then I immediately looked at my laptop and I saw that I was being logged out of Gmail, and I look back on my phone and then I saw that I had no service. Between those three things, I knew I was under attack.”
“It wasn't just startling,” he added, “it was life-altering.”

Ross, who has since started website StopSimCrime.org to raise awareness, isn’t alone. According to David Berry, a task force agent with the REACT Task Force -- a partnership of local, state and federal agencies, and the private industry, that’s taking on the escalating problem of high-technology crime -- more than $50 million has been stolen through swapping SIM cards in mobile phones within the last three years.
What is SIM swapping?
A form of identity theft, subscriber identity module (SIM) swapping, is when a hacker switches your phone number to another SIM card in the hacker's phone, often by contacting your phone provider and using trickery or other means.
“They'll just call up somebody at a store and they'll convince them that maybe they're the customer,” Berry said. “They'll also get people that are that are willing to do it for money, so they'll basically bribe employees.”
Once the hacker has access to your number, they can use it to reset your passwords on accounts it’s linked to, such as emails, social media and some mobile payment services.
“Our phone number is basically our identity and the security of a lot of our other accounts are backed up by being able to get a message to our phone number,” Berry said.
Eric Taylor, a hacker turned cybersecurity expert, says SIM card crimes are one of the easiest ways for hackers to crack into someone’s personal accounts. In a demonstration, Taylor was able to use prompts to reset an Instagram account’s password in a matter of seconds without even knowing the username.
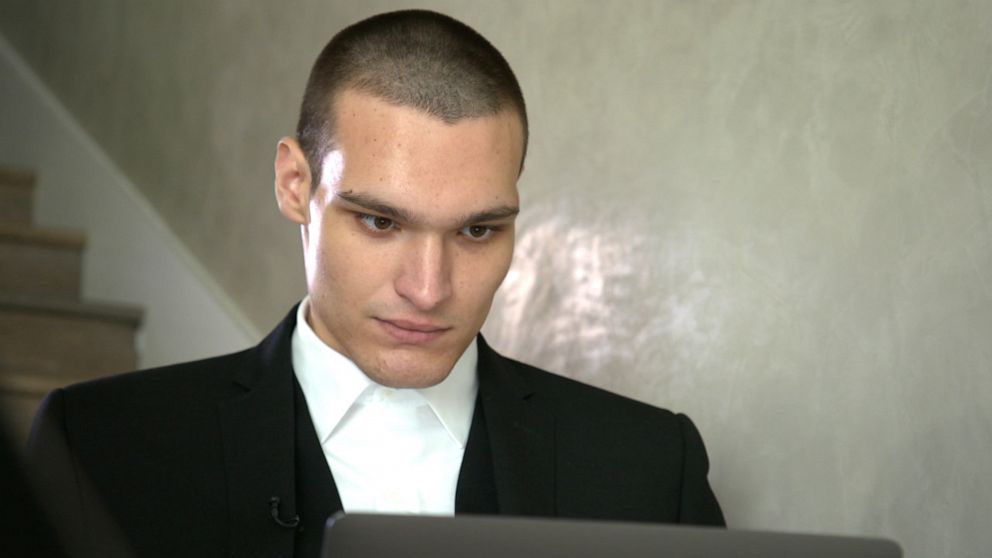
“I can change the [account’s] phone number, and take it off and put my own email and completely just take over the account,” he said, replicating the process on Twitter and Gmail.
Instagram recommends that its users enable two-factor authentication using a third-party authenticator app that does not rely on a text message verification. Google further recommended customers take its Security Checkup “for added protection” for accounts with the service.
Last month, the FBI sent out a security advisory warning businesses about the growing problem of SIM swapping.
CTIA, the Wireless Association, and major phone providers such as AT&T, T-Mobile, Verizon and Sprint, recommend customers add an extra layer of protection for themselves by using strong PIN numbers and passwords to their accounts.
What can you do to protect yourself?
First, smartphone users can add a layer of protection by using a third-party authenticator app, such as Google Authenticator and Authy. These apps allow for two-step authentification, but instead of sending the alert to your phone number, they will send it to the app.
Additionally, check with your mobile service provider to see if they offer the option of adding an extra password or personal identification number (PIN).
It is also recommended that you don’t use the same passwords and PINs for your different accounts.
Law enforcement and the American Bankers Association don’t see SIM swapping as a threat to traditional banks as the majority of reported cases involve cryptocurrency accounts, but you may want to be careful when linking your phone number to mobile payment apps such as Venmo or PayPal.
What should you do if it happens to you?
If your identity is compromised by a SIM-swapping hacker, the first thing to do is to call your mobile service provider and report it. Try to get them to disconnect the now-stolen phone number immediately.
Also, check all of your accounts that are linked to the stolen phone number. Change the passwords and PINs, and delete that number from those accounts. If one of those accounts has been breached, contact that company as soon as possible.
Also, be sure to visit IdentityTheft.gov and complete the steps necessary to report that your identity has been stolen.